In this Blog, we will explore the most common post-migration cloud security gaps, including misconfigurations, identity and access management risks, visibility challenges, compliance drift, and cost-security tradeoffs. We’ll also examine why operations teams struggle after migration and outline practical strategies to strengthen cloud security posture, improve monitoring, and ensure long-term resilience.
Cloud migration is usually seen as the finish line. Companies spend months designing architecture, planning data migration and application modernisation, choosing a cloud vendor, and assessing various cloud migration approaches, such as lift-and-shift, replatforming, and refactoring. After migrating workloads to cloud platforms, companies mark the completion of the journey as a significant accomplishment.
However, the truth is quite different.
Most cloud migrations fail during the migration process. Instead, they fail after the migration process, in the Day-2 operations phase, where cloud management, governance, security, compliance, identity, and cost management determine the success or failure of cloud investments.
The key to cloud success is scalability, flexibility, business continuity, and innovation. But without proper operational management, the cloud environment’s own flexibility can lead to misconfigurations, unmanaged costs, fragmented identity and access management, and vulnerabilities to unauthorized access to digital assets.
Day-2 operations are the point where operational discipline either evolves or fails. They determine whether companies change the way they do business with cloud technology or simply move the same old inefficiencies to a new infrastructure paradigm.
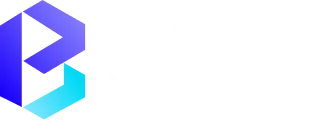
Understanding Day-2 Operations in Cloud Migration
Day 2 operations are the lifecycle of cloud management after the initial deployment. While Day 1 is about the execution of the cloud migration strategy, whether it is lift and shift, hybrid, or cloud-native, Day 2 ensures that the workload is secure, optimized, compliant, and aligned with business goals.
The cloud infrastructure is not static. Resources are dynamically scaled, services are updated, and regulatory needs keep changing. This makes it imperative to have a constant watch to maintain security, cost efficiency, and stability.
This is the stage where it is determined whether the benefits of the cloud or just the same inefficiencies are carried forward to the new cloud infrastructure.
Definition of Day-2 Operations
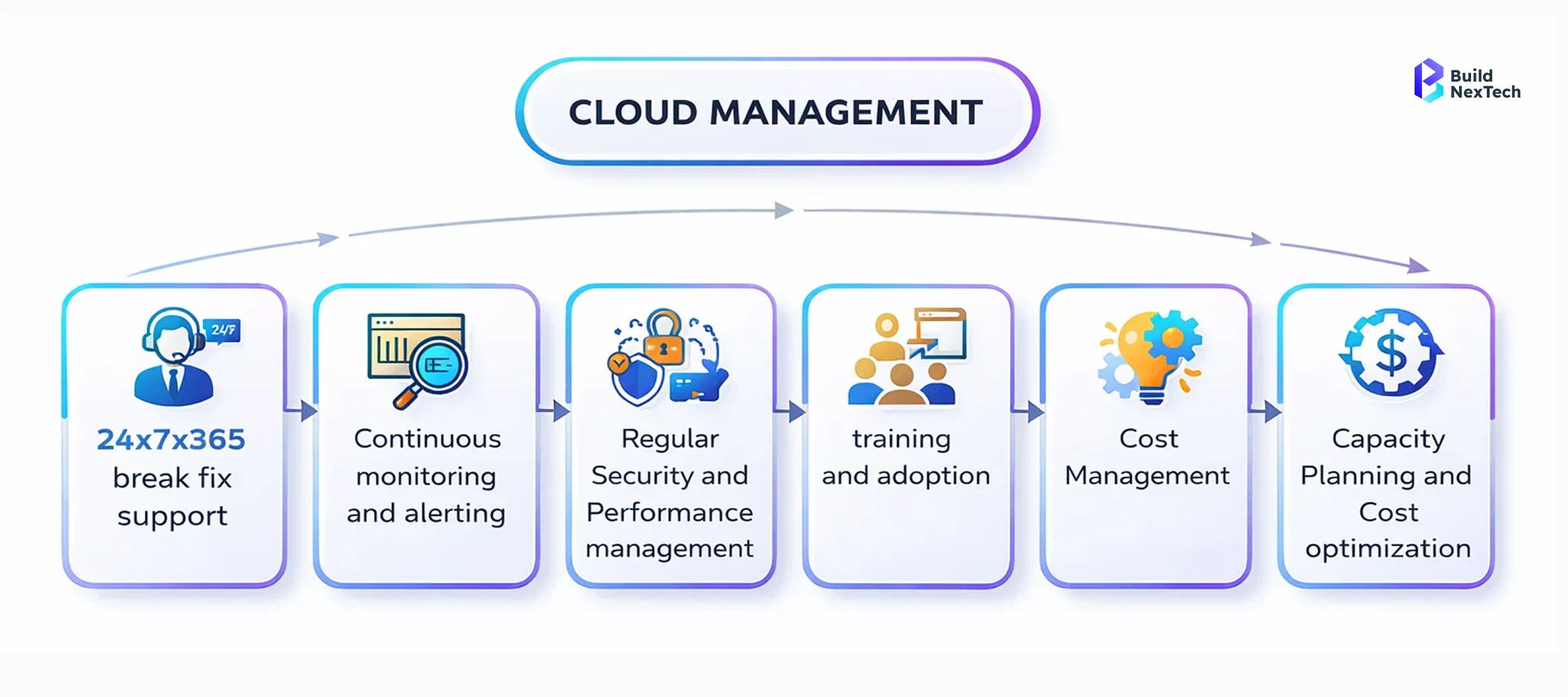
Day 2 operations include all activities necessary after migration to ensure optimal functioning of cloud services. These activities include:
- Cloud infrastructure monitoring
- Identity and access management
- Multi-factor authentication enforcement
- Security policy enforcement
- Validation of regulatory compliance, including ISO 27001
- Performance optimization
- Cost optimization and forecasting
- Incident response and business continuity planning
- Automation and DevSecOps optimization
Day 2 operations are not like migration, which is a one-time process. Day 2 operations are continuous.
Common Challenges in Day-2 Operations
Some of the common points of failure include:
- Security drift after go-live
- Inconsistent ownership between IT, DevOps, and security teams
- Insufficient centralized observability for hybrid environments
- Over-provisioned compute and storage
- Identity and access management sprawl
- Poor enforcement of multi-factor authentication
- Inconsistent governance across cloud services
- Alert fatigue from fragmented monitoring tools
These points of failure compound. Often, the organization underestimates how quickly identity management misconfigurations and unclear shared responsibility can introduce risk.
Cloud Security Risks in Day-2 Operations

The cloud infrastructure after migration is dynamic and distributed. There is interaction between various cloud platforms, data flows between cloud services, and APIs are used to integrate internal and external systems. This increases the risk of exposure if there is no proper governance.
The risk of security in Day-2 operations is rarely experienced as a catastrophic incident. It is usually experienced as a gradual process of small security misconfigurations, overly permissive security, inconsistent identity and access management policies, and ambiguity in the boundaries of shared responsibility between the organization and the cloud provider.
Top 10 Cloud Security Risks
- Misconfigured storage buckets with exposed digital assets
- Overly permissive IAM roles leading to unauthorized access
- Failure to enforce multi-factor authentication
- Unencrypted data at rest or in transit
- Unsecured APIs connecting cloud services
- Insider threats from inadequate identity governance
- Poor network segmentation across cloud platforms
- Insufficient logging and monitoring visibility
- Gaps in multi-cloud security visibility
- Misconceptions about the shared responsibility model
These cloud security risks are more likely the result of operational oversights rather than complex attacks.
Data Security Risks in Cloud Computing
Data security is still one of the most critical factors for success in the post-migration process. The risks are as follows:
- Unintentional exposure of data
- Inadequate management of encryption keys
- Ineffective data backup and disaster recovery plans
- Unsuccessful fulfillment of regulatory compliance requirements
- Unsound data retention and deletion practices
Cloud security operations should be made compliant with regulatory requirements such as ISO 27001 and industry-specific requirements. Data assets should be safeguarded against unauthorized access through continuous auditing and identity management enforcement.
Best Practices for Cloud Security Operations
To improve security posture:
- Enforce least privilege identity and access management
- Implement multi-factor authentication on all critical accounts
- Enforce zero-trust architecture guidelines
- Automate configuration and compliance scans
- Centralize logging for all cloud platforms
- Perform vulnerability scans on a regular basis
- Define shared responsibility ownership between in-house teams and the cloud vendor
Security has to be an integral part of cloud operations, and it cannot be a static checklist.
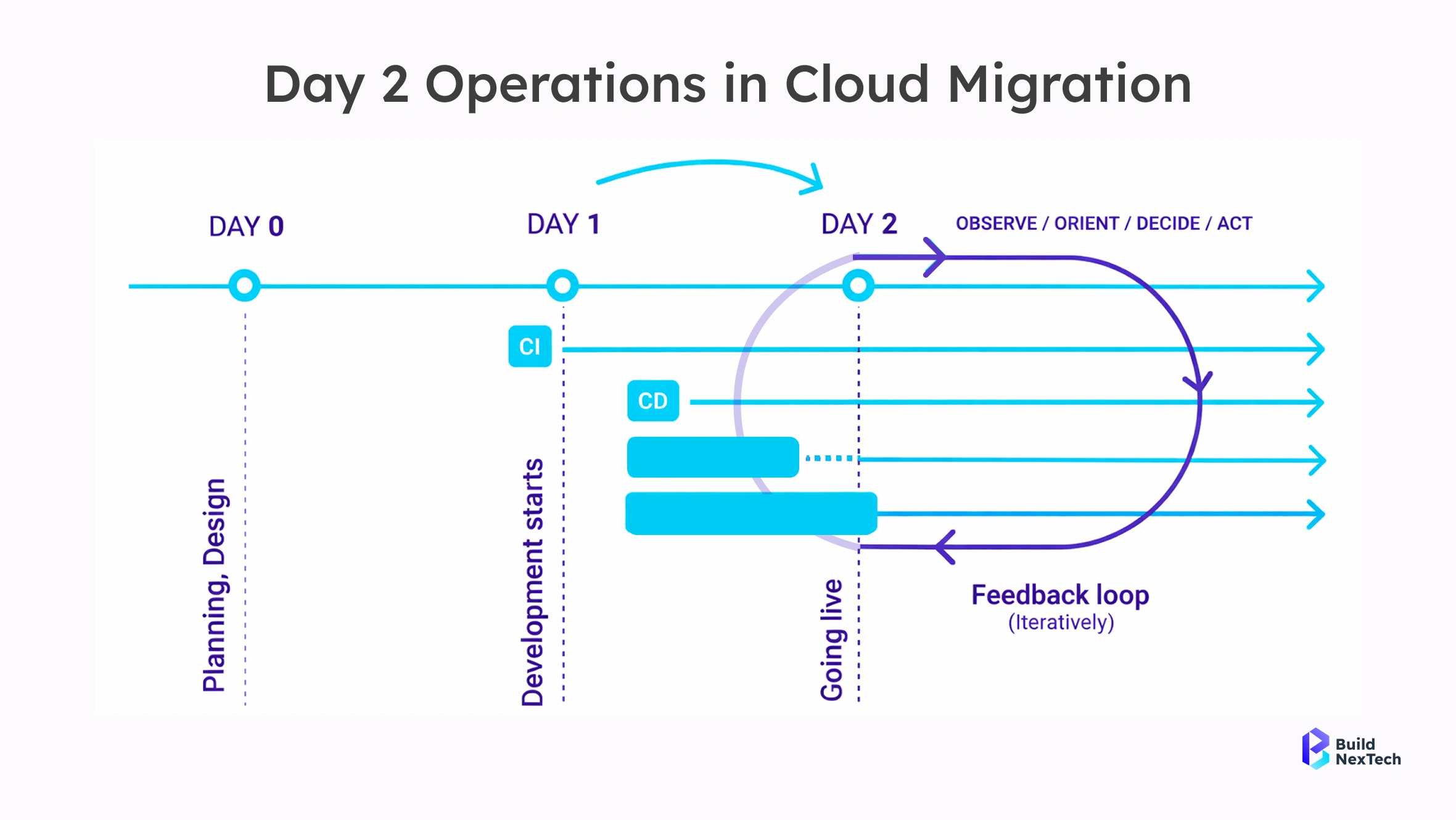
Cost Overruns and Optimization Gaps in Cloud Operations
Cost savings are one of the strategies that cloud migration may use. But in the absence of governance, the agility of cloud services may result in unmanaged growth.
Cloud spending varies dynamically, unlike traditional infrastructure. Scaling, storage, data migration traffic, and inter-platform interactions cause unpredictable variations in monthly expenses.
Day-2 cost discipline helps in realizing cost agility or cost shocks that can disrupt business.
Cloud Cost Optimization Best Practices
Best practices are:
- Rightsizing compute resources
- Removing idle workloads
- Automating shutdown of development environments
- Using tagging standards for cost allocation
- Using reserved pricing models
- FinOps collaboration between finance and engineering teams
Cost optimization: Cloud solutions should provide cost savings.
Best Cloud Cost Optimization Tools
Today’s optimization platforms offer the following:
- Real-time cost visibility across cloud platforms
- Budget alerts and anomaly detection
- Usage forecasting
- Department-level allocation reporting
- Resource utilization analytics
The tools are meant to improve visibility, but financial prudence and governance are the drivers of success.
Implementing Managed Cloud Infrastructure for Cost Savings
Cloud services are managed in a way that benefits the organization by:
- Monitoring expenditure trends
- Modifying scaling rules
- Improving storage designs
- Predicting future usage
A structured approach to operations enables the management of cloud expenditure to shift from firefighting to financial management.
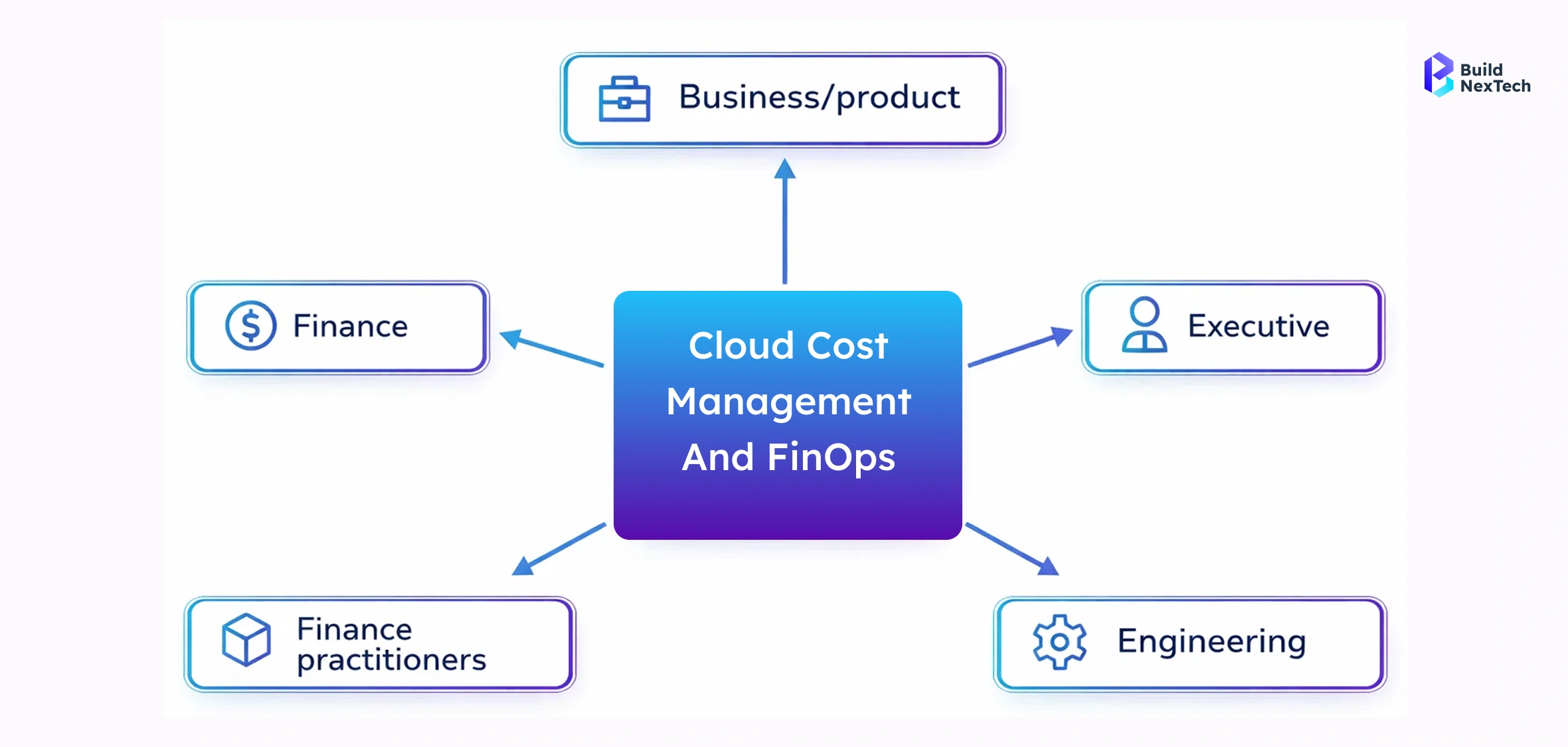
Hybrid and Multi-Cloud Operational Complexity
Most businesses run in a hybrid and multi-cloud environment. Although this enhances redundancy and flexibility, it also leads to fragmentation.
Each cloud service can have its own identity management system, compliance reporting tools, and security settings. This makes governance challenging.
Understanding Hybrid Cloud Models
Hybrid cloud refers to the integration of on-premise infrastructure with public cloud infrastructure. Multi-cloud involves the distribution of workloads across multiple cloud services.
Benefits include:
- Diversification of vendors
- Ability to adapt to geographic compliance requirements
- Improved business continuity
- Workload optimization
But it also has complexities that demand mature management.
Security Challenges in Hybrid Cloud Environments
Hybrid risks are:
- Fragmented visibility
- Inconsistent identity and access management
- Complexity of identity federation
- Increased attack surfaces
- Inconsistent cross-platform compliance
Security policies must be consistent across environments
Best Practices for Hybrid Cloud Security Operations
- Centralize identity management
- Enforce consistent compliance standards
- Automate cross-cloud audits
- Use unified monitoring tools
- Use shared responsibility clarity
Hybrid maturity requires discipline in orchestration.
Governance and Compliance in Day-2 Cloud Operations
Governance is the framework that provides the structural support for effective Day 2 cloud migration strategies. Without well-articulated policies, ownership, and accountability, cloud systems tend to become inconsistent.
Compliance pressures for ISO 27001 certification and data protection regulations in industries further increase the complexity.
Establishing a Cloud Governance Model
A governance model specifies the following:
- Resource provisioning standards
- Identity and access management controls
- Cost accountability frameworks
- Compliance reporting mechanisms
- Security baseline enforcement
Governance ensures operational stability in cloud services
Shared Responsibility Model in Cloud Services
Within the shared responsibility model, the following applies:
- The cloud provider is responsible for securing the infrastructure
- The customer is responsible for securing data, identity management, access controls, and applications
This helps to avoid any accountability gaps.

The Role of Managed Cloud Services in Strengthening Day-2 Operations
As cloud infrastructures grow, it may become difficult for in-house teams to ensure a consistent level of observation across cloud platforms. Managed cloud services offer expertise, tools, and reinforcement of best practices.
They help organizations move from a reactive approach to troubleshooting to a proactive approach to optimization.
What Are Managed Cloud Services?
- Infrastructure management
- Cloud security operations
- Cost optimization frameworks
- Regulatory compliance monitoring
- Performance management
- Business continuity planning
These services improve the operational maturity throughout the cloud migration process.
Leveraging Managed Cloud Platforms for Success
The organizations using managed services will be able to:
- Improve their security and compliance position
- Lower operational risk
- Enhance incident response times
- Achieve predictable cost savings
- Enforce better governance
Partners like Buildnextech help organizations improve their cloud security, identity, compliance, and cost positions post-cloud migration. Buildnextech, by emphasizing structured Day-2 frameworks, ensures that the cloud solutions are secure, scalable, and optimized even after the initial deployment.
Future Trends in Cloud Management and Security
Emerging trends include:
- AI-driven security analytics
- Zero-trust architectures
- DevSecOps integration
- Automated compliance monitoring
- Advanced observability across cloud platforms
Day-2 operations are evolving toward automation-first governance models.
Conclusion
It is in Day-2 operations that the success of the cloud is either cemented or, in many cases, quietly eroded. While it is common for organizations to celebrate the achievement of migration milestones, the hard work begins once the workload is up and running, and business operations are dependent on the reliability of the cloud.
The cloud security, identity and access management, cost optimization, regulatory compliance, and governance of the cloud post-migration will determine whether digital assets are still safeguarded against unauthorized access and whether cost savings are maintained.
Cloud transformation is not a project but an ongoing operation. By integrating sound governance models, enforcing multi-factor authentication, ensuring clarity on shared responsibility, structuring cloud migration, and tapping into expert knowledge from partners such as Buildnextech, organizations can ensure that operational failures are avoided.
The bottom line is that businesses need to move from “migration complete” to “cloud operations optimized.” Organizations that focus on Day-2 excellence can fully leverage the cloud, enhance security and compliance, improve business continuity, and optimize return on investment.
People Also Ask
1. What do Day-2 operations in cloud computing mean?
Day-2 operations are the management, monitoring, optimization, and governance processes that take place after the initial cloud migration. These processes ensure long-term security, performance, and cost optimization.
2. What are the most significant security risks in cloud computing?
The most significant risks are misconfiguration, over-permissive access controls, insecure APIs, data breaches, lack of monitoring, and confusion about the shared responsibility model.
3. How can businesses optimize costs in the cloud?
Businesses can optimize costs by rightsizing resources, removing idle resources, enforcing tagging policies, using reserved instances, adopting FinOps, and continuously analyzing usage patterns.
4. What is the importance of managed cloud services in security?
Managed cloud services offer continuous monitoring, vulnerability management, compliance, and incident response capabilities, which improve overall security posture.











.png)






.webp)
.webp)
.webp)