Over the past few years, cloud-related security incidents have continued to rise, with misconfigurations, identity-based attacks, and supply chain vulnerabilities becoming leading causes of breaches. As organisations expand their digital footprint across cloud platforms, the attack surface grows just as quickly. What was once considered an IT concern is now a board-level priority.
Cloud security has become one of the main pillars of organisational resilience. In today’s highly sophisticated threat landscape, behaviours such as identity-based attacks, supply chain attacks, and advanced persistent threats are no longer rare occurrences. This shift has forced security leaders to reassess their strategies and move beyond reactive defence toward a proactive, intelligence-driven security posture.
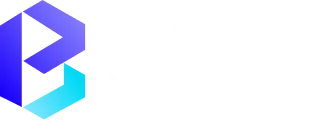
The Cloud Security Maturity Model has emerged as a vital tool that helps the organisation assess its security posture, understand the risks, and enhance the overall cloud security posture. By adhering to the guidelines set by the NIST Cyber Security Framework and NIST 800-53, the organisation can shift from a reactive security posture to a preemptive security posture.
In this blog, we will explore what the Cloud Security Maturity Model is, why it matters, the key challenges organisations face in cloud environments, best practices for strengthening security foundations, secure cloud migration strategies, cost optimization without compromising protection, and how advanced cloud and hybrid security approaches can help organisations build long-term resilience.
Organisations can also explore practical implementation insights in BNXT’s cloud security best practices guide to strengthen their approach.
Understanding the Cloud Security Maturity Model
In order for the organisation to enhance the cloud security posture, it is first imperative for the organisation to understand the concept of maturity and how the organisation can utilize the metrics for the purpose of enhancing the overall cloud security.
The Cyber Security Maturity Model helps the organisation assess the overall security posture and develop a roadmap for the purpose of enhancing the overall security posture.
For organisations starting their maturity journey, resources from BuildNexTech can provide additional guidance on aligning security strategy with business goals.
What is the Cloud Security Maturity Model?
Cloud Security Maturity Model is a framework that is used to assess the effectiveness of how an organisation manages their attack surfaces, vulnerability management practices, as well as threat detection practices. It incorporates asset inventory management, asset discovery management, as well as data classification management.
As organisations progress through maturity stages, they adopt advanced capabilities including:
- Threat intelligence integration
- Behavioural analytics and predictive analytics
- Continuous threat monitoring
- Risk-based prioritization of remediation
These capabilities help organisations better defend against cyber threats while strengthening their security operations.
Why organisations Adopt a Maturity Model
Organisations use maturity models for achieving clarity on their security status and for effective prioritisation. Due to the rise in regulatory requirements and the dynamic regulatory environment, organisations are now adopting maturity models for effective regulatory compliance and improved efficiency.
By taking the maturity-driven approach, organisations can:
- Stronger alignment between security strategy and business risk scoring
- Improved coordination across security teams and support teams
- Better visibility into the attack surface map
- Enhanced readiness for breach and attack simulation exercises
Building a Strong Cloud Security Foundation
A strong foundation is vital for the defence of the cloud estate, especially with the increased adoption of SaaS, automation platforms, and AI infrastructure, which utilize generative artificial intelligence and large language models.
Key Cloud Security Challenges
In modern organisations, there is a growing threat landscape, including environments in multiple clouds, remote working, and interconnected supply chains. Asset discovery and asset inventory are critical in managing the threat landscape, otherwise, it becomes a challenge to maintain a clear view of the environment.
The main challenges in managing the threat landscape are:
- Dealing with security risks in multiple cloud environments, including Google Cloud
- Dealing with identity-based attacks through proper IAM policies
- Ensuring encryption settings meet compliance standards
- Monitoring IP address exposure and network vulnerabilities

Essential Cloud Security Best Practices
To address these challenges, organisations must implement cloud-native security controls that align with industry frameworks.
Core best practices include:
- Implementing strong vulnerability management programs
- Using SIEM solutions and XDR platforms for threat monitoring
- Establishing incident response processes for rapid containment
- Leveraging threat hunting and threat hunt exercises
- The application of data classification to protect sensitive information
These strategies will improve the organisation's overall security.
Secure Cloud Migration Strategies
With the increasing cloud migration strategy within an organisation, there is a need to incorporate security into all phases of the cloud migration process.
Planning a Secure Cloud Migration
To plan a secure cloud migration strategy, there is a need to understand the organisation's attack surface and security controls by mapping the organisation's assets, regulatory needs, and adversarial simulations.
Organisations should focus on:
- Conducting a security maturity assessment
- Aligning controls with NIST Cybersecurity Framework guidelines
- Implementing continuous threat exposure management
- Ensuring proper identity and access configurations
Key Cloud Migration Tools and Services
Modern migration tools support security by providing visibility into workloads and enabling attack simulation and breach and attack simulation exercises. These tools also help organisations validate security metrics and ensure consistent enforcement of policies across environments.
Cloud Cost Optimization Without Compromising Security
Optimizing costs while maintaining robust security requires balancing efficiency with risk management. A well-governed environment reduces unnecessary resources while maintaining strong security controls.
Cost Management Best Practices
Organisations can achieve cost efficiency by combining automation platforms with business risk scoring models to prioritize high-impact risks.
Effective practices include:
- Rightsizing resources based on usage data
- Automating monitoring through predictive analytics
- Aligning budgets with security operations priorities
- Using reference number tracking for compliance reporting

Leading Cloud Cost Optimization Platforms
Cost optimization platforms integrate with SIEM solutions and XDR platforms to provide a unified view of performance, costs, and security risks. These insights help organisations maintain strong security posture while improving financial efficiency.
Leveraging Cloud Security Services
As cyber threats become more sophisticated, many organisations rely on specialized services to enhance their internal capabilities and maintain continuous protection.
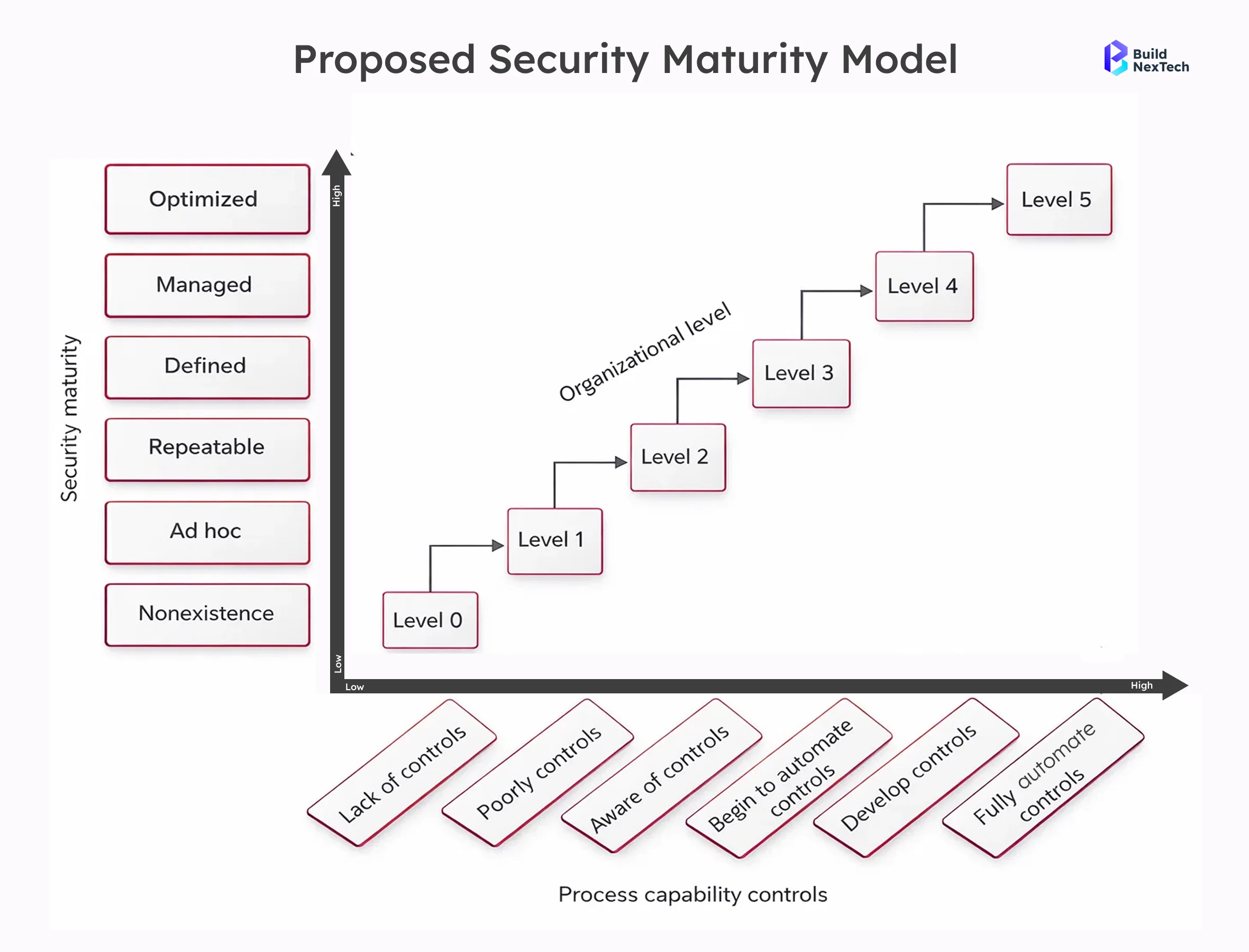
Types of Cloud Security Services
Cloud security services deliver advanced protection through integrated technologies and expert oversight.
Common services include:
- Threat intelligence and threat monitoring
- Continuous threat exposure management
- Managed detection and response
- Breach and attack simulation programs
- Identity and access governance
These services help organisations stay ahead of adversaries and improve overall security maturity.
Selecting the Right Cloud Security Provider
The selection of the right provider involves technical and strategic criteria. It is important for security leaders to assess the extent to which the provider supports automation and detection capabilities.
A good provider should have expertise in managing the ever-changing cyber threats and regulatory needs.
Advanced Security for Azure and Hybrid Environments
Hybrid and multi-cloud environments need policies and centralized monitoring to achieve a seamless security solution across the entire cloud environment.
Azure Security Tools and Best Practices
Cloud computing technology provides security tools that enable an organisation to implement policies, monitor threats, and maintain regulatory compliance. Guidance from Microsoft Azure Security documentation can help organisations implement these controls effectively.
Hybrid Cloud Security Considerations
Hybrid cloud environments present an additional layer of complexity because the security solution needs to work seamlessly across the entire environment.
The key areas of concern include:
- Maintaining a unified attack surface map
- Implementing identity-based security controls
- Conducting adversarial simulations to test resilience
- Ensuring consistent threat detection capabilities
Conclusion
Cloud security maturity is not an event, but rather a continuous process. It demands the alignment of technology, processes, and people. The introduction of new technologies like AI infrastructure and automation solutions necessitates the need for organisations to have an effective proactive security posture.
Key Takeaways: Moving from Reactive to Proactive Security
Using maturity models allows organisations like those in the list of organisations above to have the capability to predict potential cyber attacks. This allows them to transition from reactive security to proactive security.
Why Continuous Maturity Improvement Matters
Continuous maturity improvement is essential to an organisation as it ensures that it is always on its toes despite the changing nature of security threats. By using threat intelligence, behavioural analytics, and predictive analytics, an organisation can always be one step ahead of potential security threats.
How BNXT Can Help Strengthen Your Cloud Security Journey
Improving cloud security maturity requires more than tools — it demands the right strategy, expertise, and continuous execution. BNXT supports organisations at every stage of their cloud security journey by combining technical depth with business alignment.
How BNXT adds value:
- Conducting comprehensive cloud security maturity assessments
- Designing risk-based security roadmaps aligned with NIST frameworks
- Implementing cloud-native security controls across multi-cloud environments
- Strengthening threat detection, monitoring, and incident response capabilities
- Supporting secure cloud migration and cost optimization initiatives
Whether your organisation is just beginning its cloud transformation or looking to enhance an existing security program, BNXT provides tailored guidance to help you move from reactive defence to proactive protection.
People Also Ask
1. How do we actually know if our cloud security is mature enough?
If your team spends most of its time firefighting alerts instead of preventing issues, that’s usually a sign there’s room to grow. Good visibility and clear processes are strong indicators you’re on the right track.
2. Why should we focus on proactive security instead of just fixing issues when they happen?
Because reacting all the time gets exhausting and expensive. When you start preventing problems early, things run smoother and surprises become much less frequent.
3. What’s the biggest thing that slows companies down when improving security?
Honestly, it’s often not the tools — it’s not knowing exactly what’s in the environment or who owns what. Once that’s clear, progress becomes much easier.
4. Does improving cloud security really make a business difference?
Yes — fewer disruptions, less risk, and more confidence from customers and leadership. It’s not just an IT win; it’s a business win.











.png)






.webp)
.webp)
.webp)